GhostLock Tool Leverages Windows API to Lock File Access Like Ransomware

Critical GitHub.com and Enterprise Server RCE Vulnerability Enables Full Server Compromise

New Vidar Malware Campaign Uses Fake YouTube Software Downloads to Steal Corporate Credentials
Claude Code, Gemini CLI, and GitHub Copilot Vulnerable to Prompt Injection via GitHub Comments

Google DeepMind Researchers Warn Hackers Can Hijack AI Agents Through Malicious Web Content
Microsoft: KB5079473 breaks internet access to Windows 11 Teams, Edge, OneDrive, Copilot [Update]

Splunk Enterprise for Windows Vulnerability Let Attackers Hijack DLLs and Gain SYSTEM Access

Google Issues Emergency Chrome Security Update to Address High-Severity PDFium and V8 Flaws
Fake CAPTCHA (ClickFix) Attack Chain Leads to Enterprise‑Wide Malware Infection in Organisations

Apple 0-Day Vulnerability Actively Exploited in Sophisticated Attack to Target Individuals

Windows Remote Access Connection Manager 0-Day Vulnerability Let Attackers Trigger DoS Attack

Windows Remote Desktop Services 0-Day Vulnerability Exploited in the Wild to Escalate Privileges

Fancy Bear Hackers Exploiting Microsoft Zero-Day Vulnerability to Deploy Backdoors and Email Stealers
Cybersecurity Weekly Newsletter – Notepad++ hack, Office 0-Day, ESXi 0-day Ransomware Attacks and More
Beware of Weaponized VS Code Extension Named ClawdBot Agent that Deploys ScreenConnect RAT

Critical Vulnerability in VM2 Sandbox Library for Node.js Let Attackers run Untrusted Code

Cisco Unified Communications 0-day RCE Vulnerability Exploited in the Wild to Gain Root Access
New Multi-Stage Windows Malware Disables Microsoft Defender Before Dropping Malicious Payloads

Attackers Abuse Discord to Deliver Clipboard Hijacker That Steals Wallet Addresses on Paste

Go 1.25.6 and 1.24.12 Patch Critical Vulnerabilities Lead to DoS and Memory Exhaustion Risks

Critical FortiSIEM Vulnerability Enables Arbitrary Commands Execution via Crafted TCP Packets

Critical FortiSIEM Vulnerability Enables Arbitrary Commands Execution via Crafted TCP Packets

FortiSandbox SSRF Vulnerability Allow Attacker to proxy Internal Traffic via Crafted HTTP Requests

Multiple Hikvision Vulnerabilities Let Attackers Cause Device Malfunction Using Crafted Packets
New OAuth-Based Attack Let Hackers Bypass Microsoft Entra Authentication Flows to Steal Keys

Threat Actor Exploited Multiple FortiWeb Appliances to Deploy Sliver C2 for Persistent Access

Scattered Lapsus$ Hunters Resurface with New RaaS Platform ‘ShinySp1d3r’ and Aggressive Insider Recruitment

Threat Actors Hacked Global Companies via Leaked Cloud Credentials from Infostealer Infections
Infostealers Enable Attackers to Hijack Legitimate Business Infrastructure for Malware Hosting
NeuroSploitv2 – AI-Powered Pentesting Tool With Claude, GPT, and Gemini models to Detect vulnerabilities

87,000+ MongoDB Instances Vulnerable to MongoBleed Flaw Exposed Online – PoC Exploit Released

Threat Actors Advertised NtKiller Malware on Dark Web Claiming Terminate Antivirus and EDR Bypass

PoC Exploit Released for Use-After-Free Vulnerability in Linux Kernel’s POSIX CPU Timers Implementation

CISA Adds ASUS Embedded Malicious Code Vulnerability to KEV List Following Active Exploitation

Microsoft Confirms Recent Windows 11 24H2/25H2 and Server 2025 Update Breaks RemoteApp Connections

Chinese Hackers Using Custom ShadowPad IIS Listener Module to Turn Compromised Servers into Active Nodes

Chrome Security Update – Patch for Critical Vulnerabilities that Enables Remote Code Execution
Notepad++ Vulnerability Let Attackers Hijack Network Traffic to Install Malware via Updates
Adobe Acrobat Reader Vulnerabilities Let Attackers Execute Arbitrary Code and Bypass Security

FortiOS, FortiWeb, and FortiProxy Vulnerability Lets Attackers Bypass FortiCloud SSO Authentication
Ransomware Targeting Hyper-V and VMware ESXi Surges as Akira Group Exploits System Vulnerabilities
Burp Suite’s Scanning Arsenal Powered With Detection for Critical React2Shell Vulnerabilities

Hackers Can Leverage Delivery Receipts on WhatsApp and Signal to Extract User Private Information

Next.js Released a Scanner to Detect and Update Apps Impacted by React2Shell Vulnerability
Cybersecurity News Weekly Newsletter – 29.7 Tbps DDoS Attack, Chrome 143, React2Shell Vulnerabilities, and Cloudflare Outage

China-Nexus Hackers Actively Exploiting React2Shell Vulnerability (CVE-2025-55182) in the Wild
Cybersecurity News Weekly Newsletter – Fortinet, Chrome 0-Day Flaws, Cloudflare Outage and Salesforce Gainsight Breach

HashiCorp Vault Vulnerability Allow Attackers to Authenticate to Vault Without Valid Credentials
Microsoft’s Update Health Tools Configuration Vulnerability Let Attackers Execute Arbitrary Code Remotely
PoC released for W3 Total Cache Vulnerability that Exposes 1+ Million Websites to RCE Attacks
Cl0p Ransomware Strikes Globally: Cox Enterprises Hit — 9,479 Users’ Data Exposed via Oracle EBS Zero-Day

Critical Vulnerability in Azure Bastion Let Attackers Bypass Authentication and Escalate privileges

Hackers Can Exploit Default ServiceNow AI Assistants Configurations to Launch Prompt Injection Attacks

Threat Actors Allegedly Selling Microsoft Office 0-Day RCE Vulnerability on Hacking Forums
W3 Total Cache Command Injection Vulnerability Exposes 1 Million WordPress Sites to RCE Attacks

Critical RCE Vulnerabilities in AI Inference Engines Exposes Meta, Nvidia and Microsoft Frameworks

CISA Warns of Fortinet FortiWeb WAF Vulnerability Exploited in the Wild to Gain Admin Access
TaskHound Tool – Detects Windows Scheduled Tasks Running with Elevated Privileges and Stored Credentials

Hackers Weaponizing Calendar Files as New Attack Vector Bypassing Traditional Email Defenses
Critical Vulnerability in Popular NPM Library Exposes AI and NLP Apps to Remote Code Execution
Cybersecurity News Weekly Newsletter – Android and Cisco 0-Day, Teams Flaws, HackedGPT, and Whisper Leak

Microsoft Entra Credentials in the Authenticator App on Jail-Broken Devices to be Wiped Out

Microsoft Teams’ New “Chat with Anyone” Feature Exposes Users to Phishing and Malware Attacks

Chrome Emergency Update to Patch Multiple Vulnerabilities that Enable Remote Code Execution

Cisco Warns of Hackers Actively Exploiting ASA and FTD 0-day RCE Vulnerability in the Wild

Attack Techniques of Tycoon 2FA Phishing Kit Targeting Microsoft 365 and Gmail Accounts Detailed
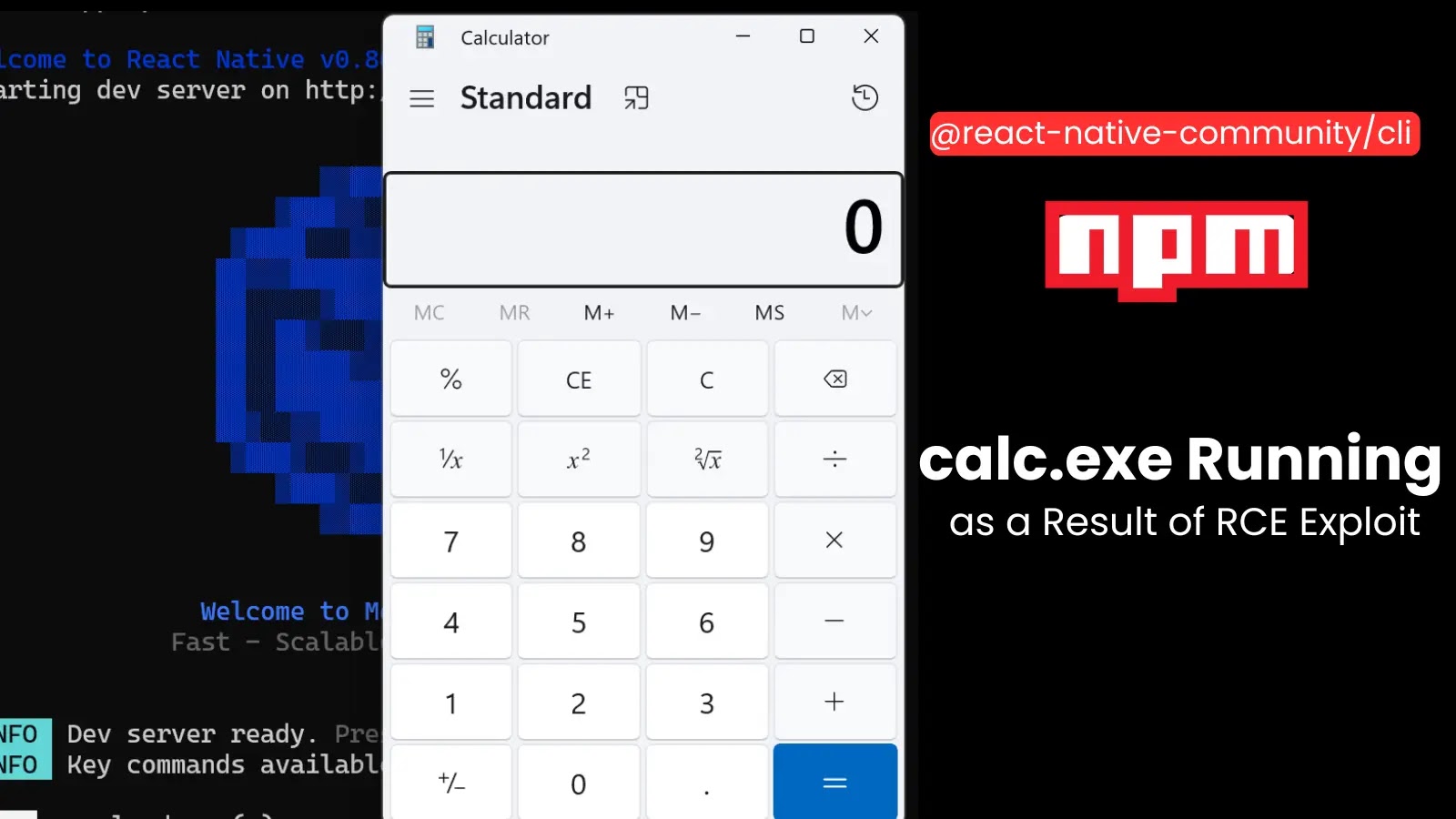
Critical RCE Vulnerability in Popular React Native NPM Package Exposes Developers to Attacks
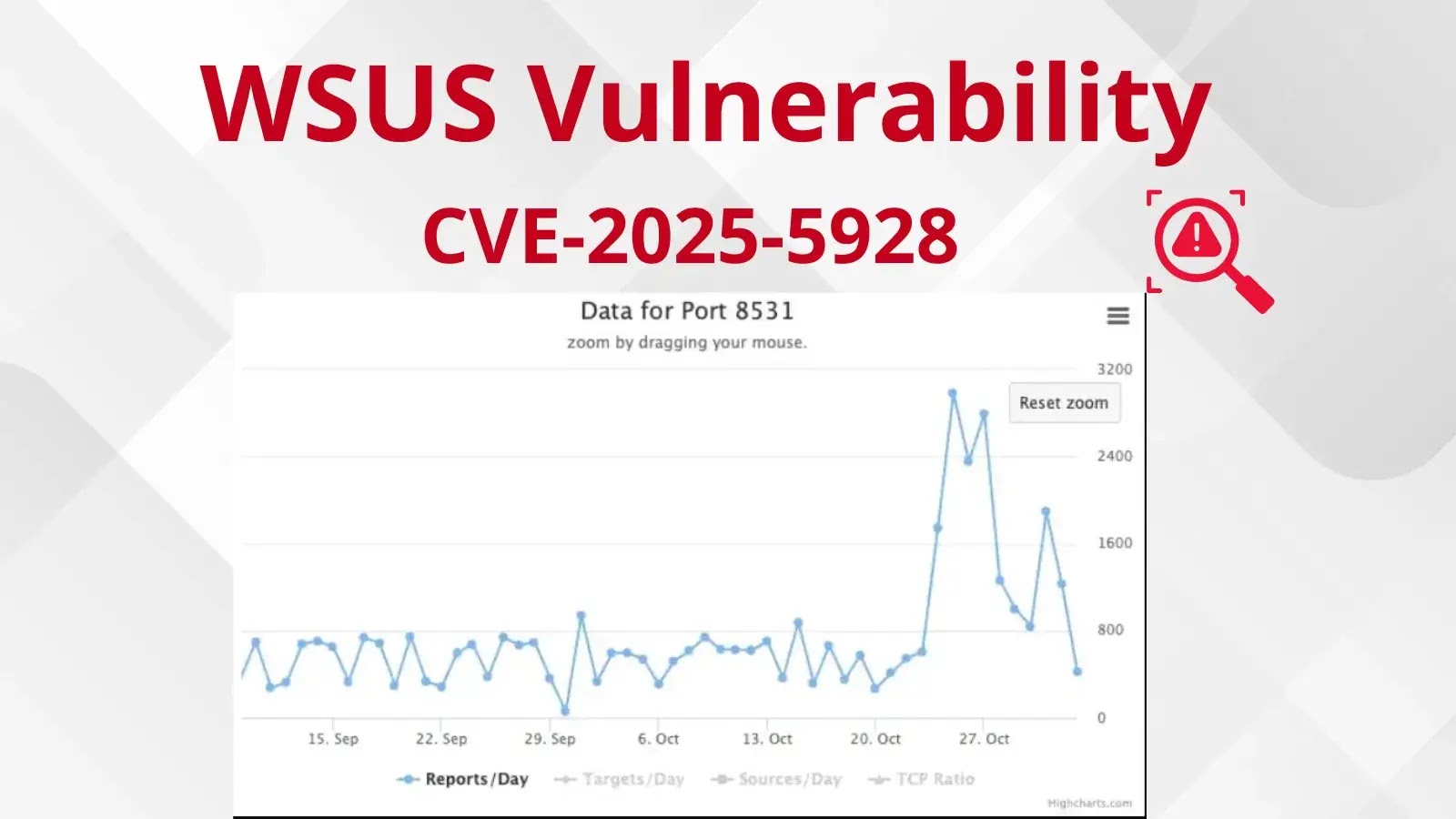
Hackers Actively Scanning for TCP Port 8530/8531 Linked to WSUS Vulnerability CVE-2025-59287

Critical Android 0-Click Vulnerability in System Component Allows Remote Code Execution Attacks
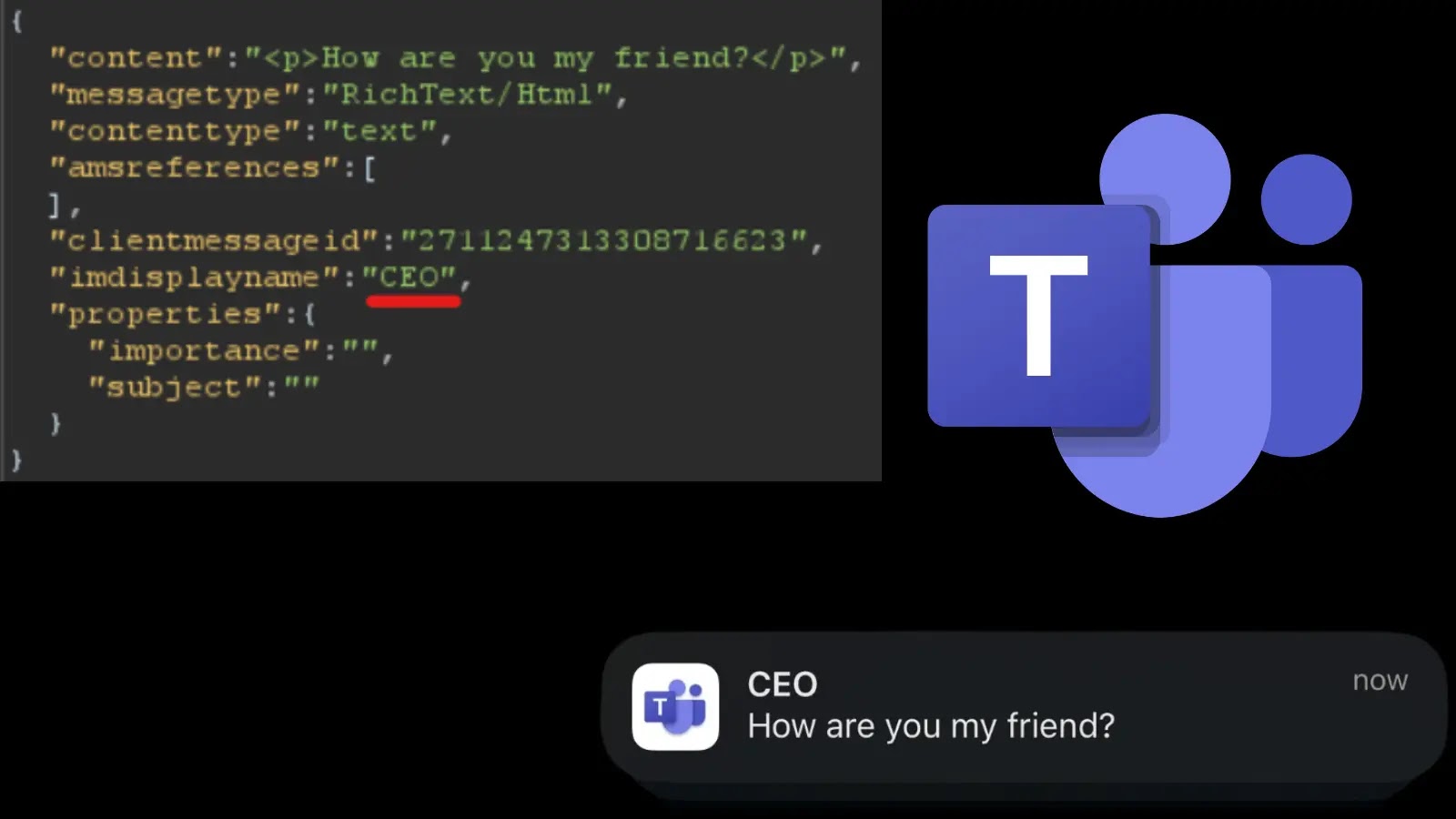
Hackers Can Exploit Microsoft Teams Vulnerabilities to Manipulate Messages and Alter Notifications
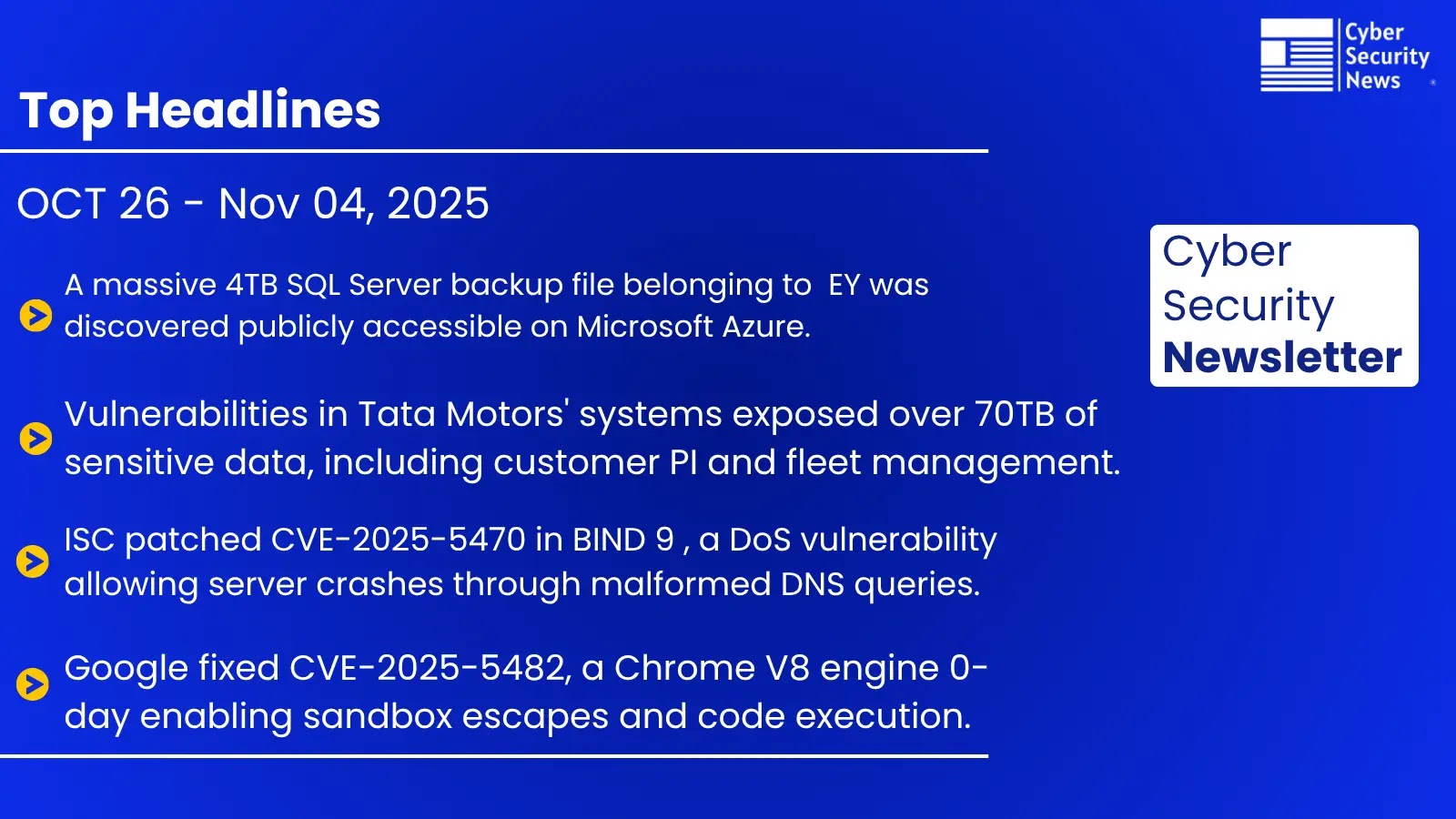
Cybersecurity News Weekly Newsletter – EY Data Leak, Bind 9, Chrome Vulnerability, and Aardvar ChatGPT Agent
CISA Warns of Linux Kernel Use-After-Free Vulnerability Exploited in Attacks to Deploy Ransomware
Cybersecurity Newsletter Weekly – AWS Outage, WSUS Exploitation, Chrome Flaws, and RDP Attacks
Hackers Exploiting Microsoft WSUS Vulnerability In The Wild – 2800 Instances Exposed Online

Hackers Abuse Microsoft 365 Exchange Direct Send to Bypass Content Filters and Harvest Sensitive Data

CISA Warns of Hackers Actively Exploiting Windows Server Update Services RCE Vulnerability in the Wild

Salt Typhoon Using Zero-Day Exploits and DLL Sideloading Techniques to Attack Organizations

Hackers Weaponizing OAuth Applications for Persistent Cloud Access Even After Password Reset

Microsoft 365 Copilot Prompt Injection Vulnerability Allows Attackers to Exfiltrate Sensitive Data

PoC Exploit Released for Windows Server Update Services Remote Code Execution Vulnerability
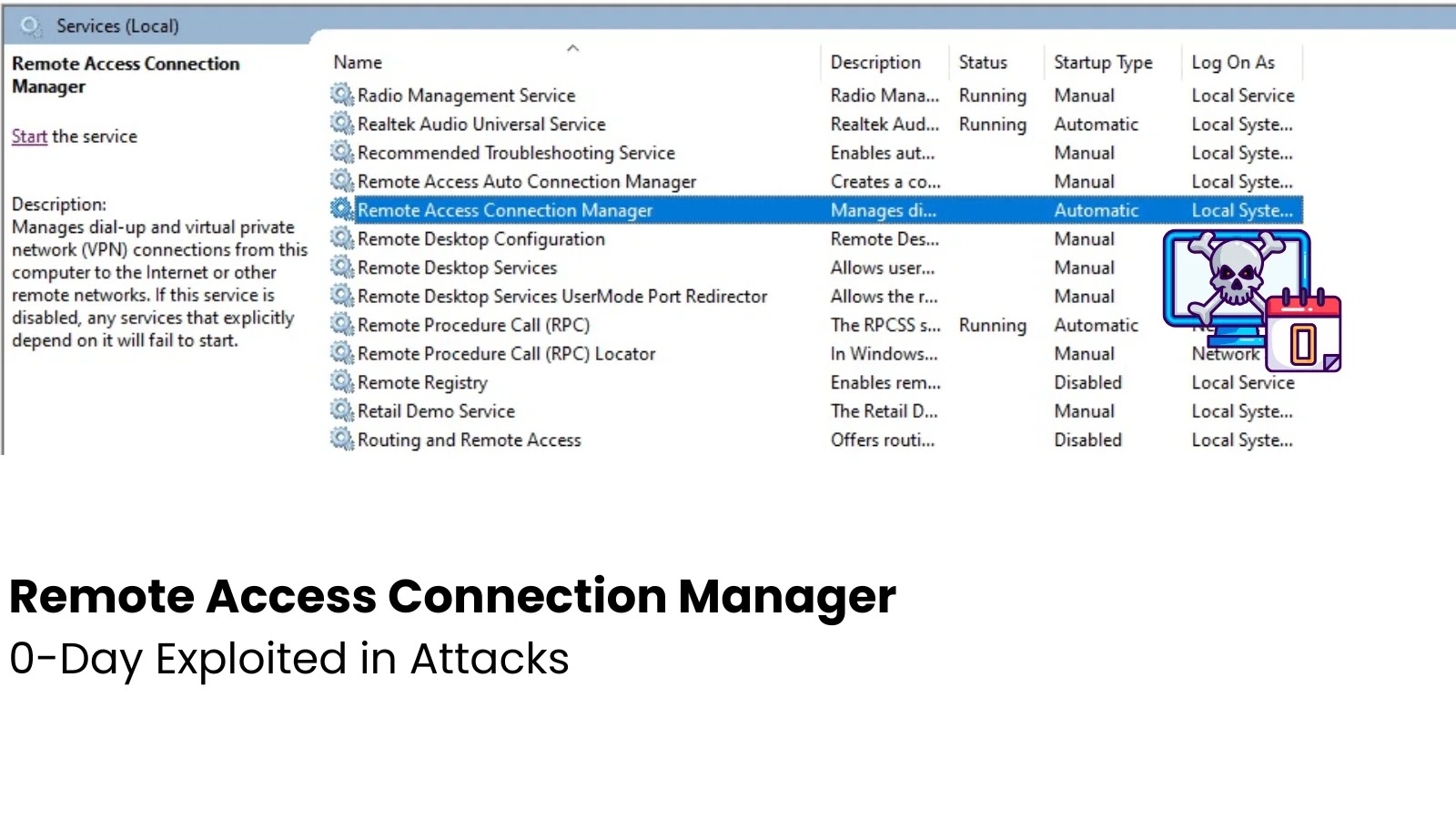
Windows Remote Access Connection Manager 0-Day Vulnerability Actively Exploited in Attacks

Microsoft Defender Vulnerabilities Allow Attackers to Bypass Authentication and Upload Malicious Files

Chrome Security Update Patches 21 Vulnerabilities that Allow Attackers to Execute Arbitrary Code

Hackers Actively Scanning to Exploit Palo Alto Networks PAN-OS Global Protect Vulnerability

OpenSSL Vulnerabilities Let Attackers Execute Malicious Code and Recover Private Key Remotely

Hackers use Weaponized Microsoft Teams Installer to Compromise Systems With Oyster Malware

Hackers Exploit WerFaultSecure.exe Tool to Steal Cached Passwords From LSASS on Windows 11 24H2

HackerOne Confirms Data Breach – Hackers Gained Unauthorized Access To Salesforce Instance

Microsoft Warns of Active Directory Domain Services Vulnerability, Let Attackers Escalate Privileges

GhostRedirector Hackers Compromise Windows Servers With Malicious IIS Module To Manipulate Search Results

Windows Defender Vulnerability Allows Service Hijacking and Disablement via Symbolic Link Attack

New Dire Wolf Ransomware Attack Windows Systems, Deletes Event Logs and Backup-Related Data

Azure Active Directory Vulnerability Exposes Credentials and Enables Attackers to Deploy Malicious Apps
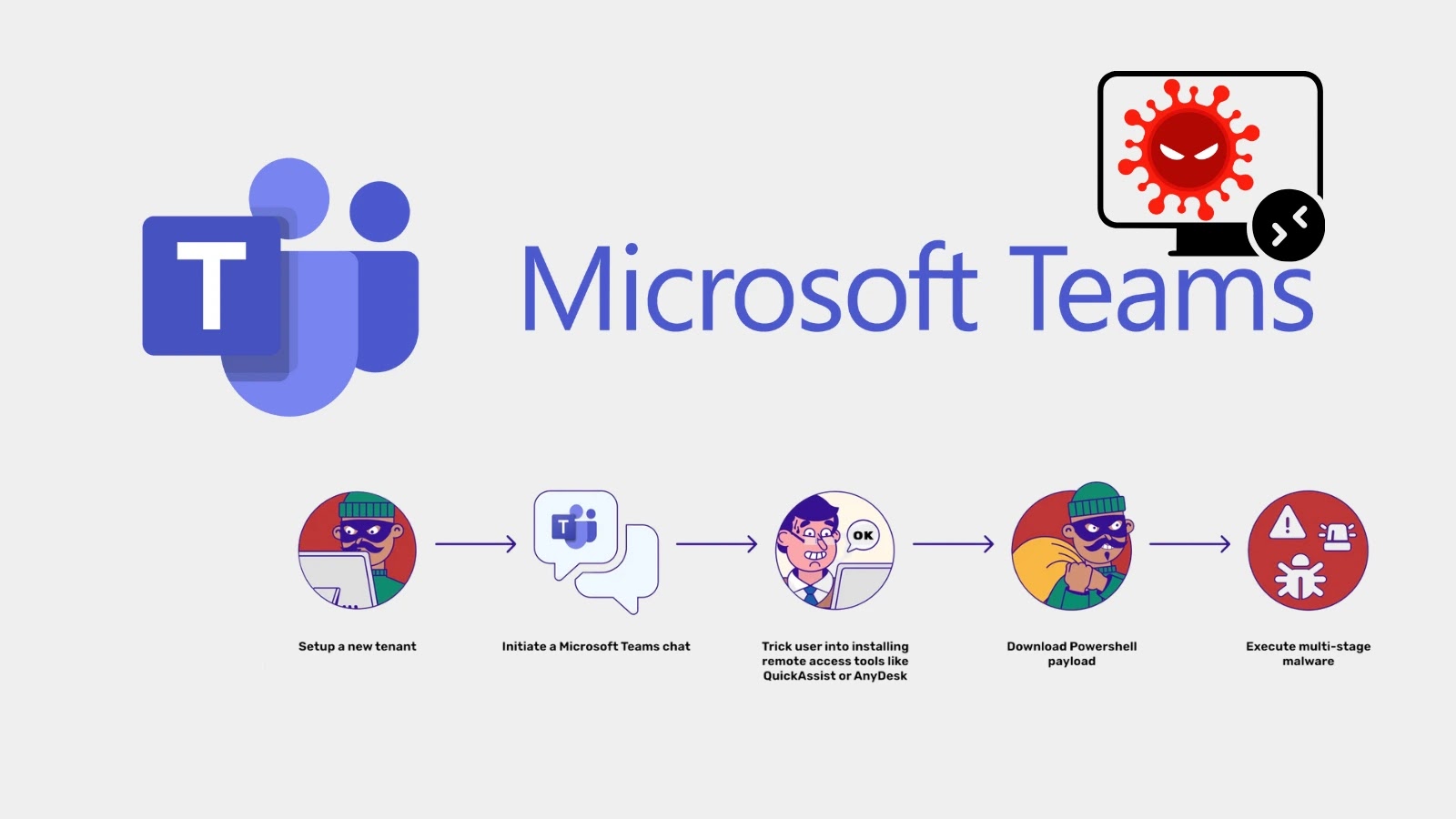
Hackers Abuse Microsoft Teams to Gain Remote Access on Windows With PowerShell-based Malware
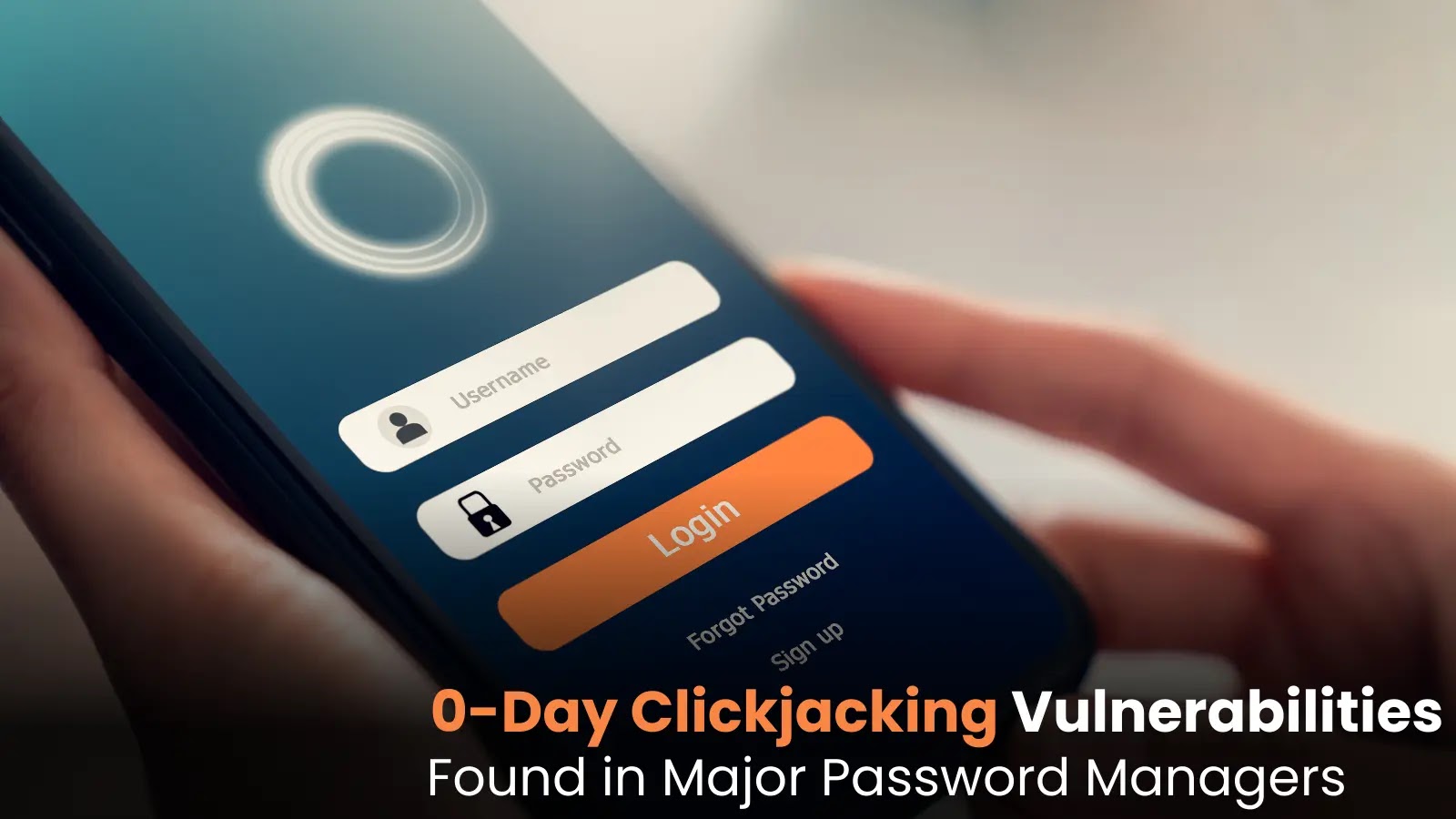
0-Day Clickjacking Vulnerabilities Found in Major Password Managers like 1Password, LastPass and Others
Microsoft Confirms August 2025 Update Causes Severe Lag in Windows 11 24H2, and Windows 10
Hackers Weaponize Active Directory Federation Services and office.com to Steal Microsoft 365 logins

New Exploit for SAP 0-Day Vulnerability Allegedly Released in the Wild by ShinyHunters Hackers
New Elastic EDR 0-Day Vulnerability Allows Attackers to Bypass Detection, Execute Malware, and Cause BSOD

Weekly Cybersecurity News Recap : Microsoft, Cisco, Fortinet Security Updates and Cyber Attacks
New ‘Win-DoS’ Zero-Click Vulnerabilities Turns Windows Server/Endpoint, Domain Controllers Into DDoS Botnet

New Active Directory Lateral Movement Techniques that Bypasses Authentication and Exfiltrate Data
Raspberry Robin Malware Attacking Windows Systems With New Exploit for CLFS Driver Vulnerability

Critical Android System Component Vulnerability Allows Remote Code Execution Without User Interaction

WAFs protection Bypassed to Execute XSS Payloads Using JS Injection with Parameter Pollution

First Known LLM-Powered Malware From APT28 Hackers Integrates AI Capabilities into Attack Methodology

New Forensic Technique Uncovers Hidden Trails Left by Hackers Exploiting Remote Desktop Protocol

TeamFiltration Pentesting Tool Weaponized to Hijack Microsoft Teams, Outlook, and Other Accounts

0-Click Microsoft 365 Copilot Vulnerability Let Attackers Exfiltrates Sensitive Data Abusing Teams
Windows SMB Client Zero-Day Vulnerability Exploited Using Reflective Kerberos Relay Attack

Wireshark Certified Analyst: Official Wireshark Certification Released for Security Professionals

Critical Linux Vulnerabilities Expose Password Hashes on Millions of Linux Systems Worldwide

Microsoft OneDrive File Picker Vulnerability Exposes Users’ Entire Cloud Storage to Websites
Vulnerability in Popular macOS App Cursor Allows Malware to Bypass Privacy Protections, Exposing User Data

Windows 11 Privilege Escalation Vulnerability Let Attackers Gain Admin Access in Under 300 Milliseconds
Hackers Exploiting Apache Tomcat Vulnerability to Steal SSH Credentials & Gain Server Control

PCI-DSS Compliance for the Retail Industry: Staying Ahead in the Era of Digital Transactions

Securing Your Operational Technology Environment: Importance of Cybersecurity and Strategies for Improvement
Enhance Your Organization’s Cybersecurity with iSecurify’s Virtual Chief Information Security Officer (vCISO) Services